How It Works
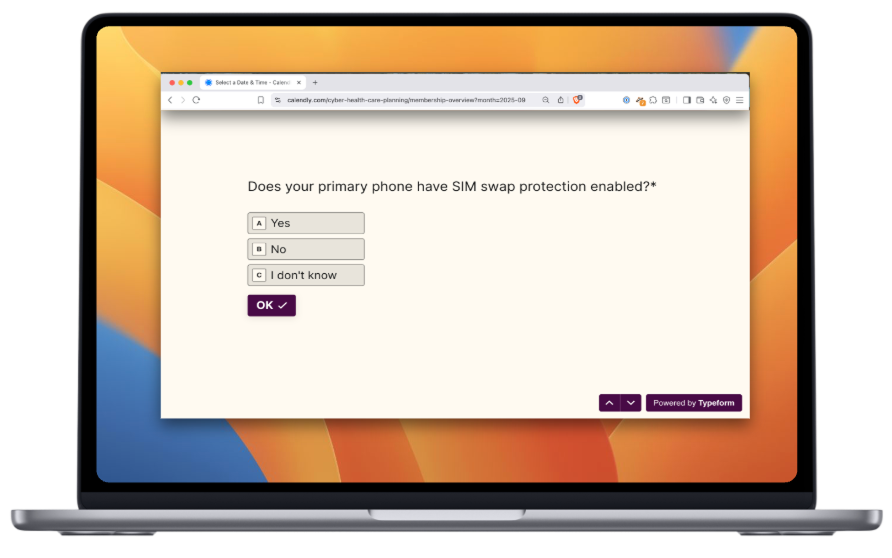
Answer questions about your posture
In order to reduce personal cyber risk, we ask a few questions about you and your current posture.
Password management, home WiFi configuration, direct reports that have access to certain accounts, goals with personal social media and more are critical understanding the shape of defense today. We do not give wholesale recommendations. Understanding your unique signature is a critical first step. It takes 10 minutes and is 100% online.
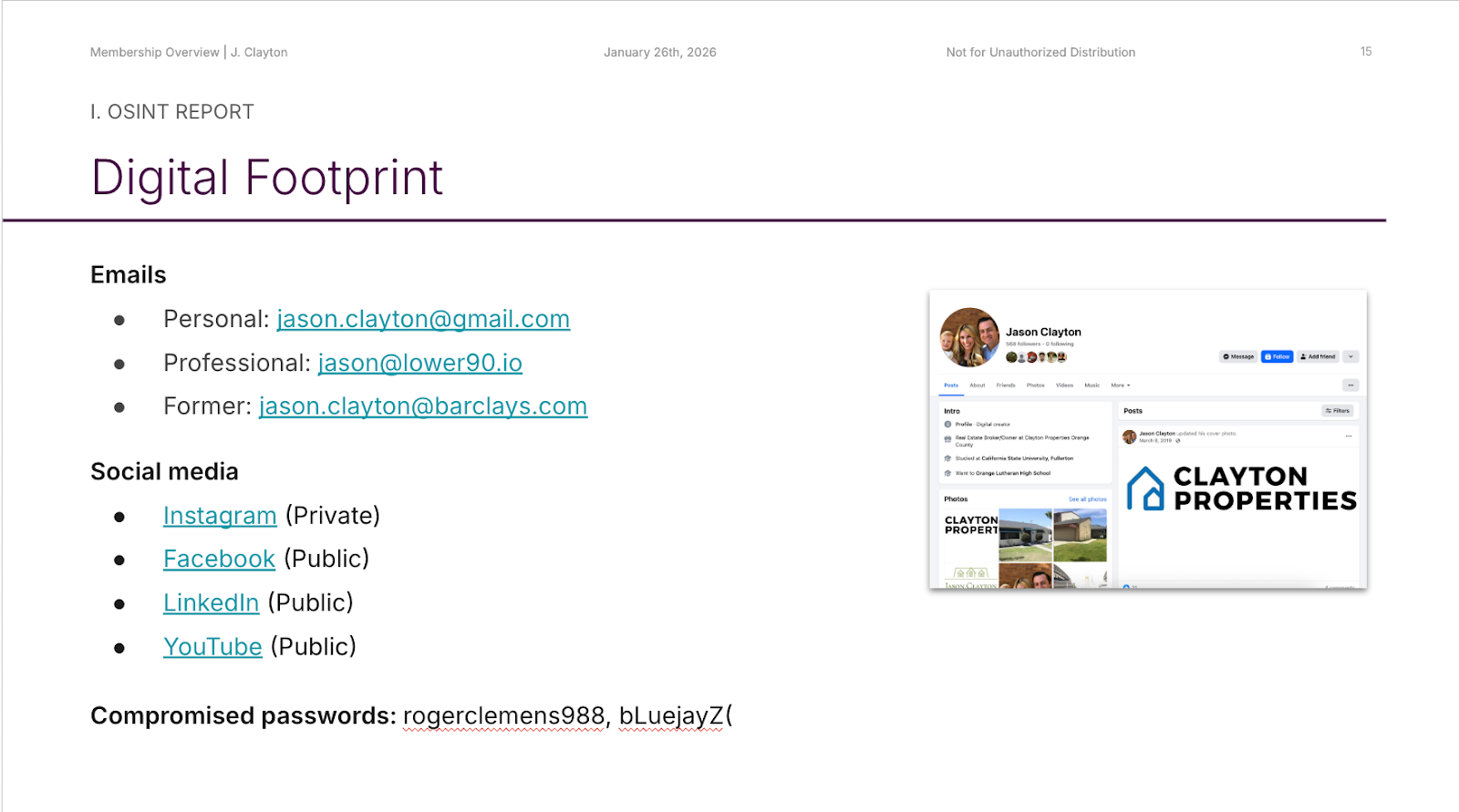
Get prospected like an attacker
We conduct an open-source intelligence research report with you as the subject.
Like opposition research in politics or a background check before a new job, we seek what someone will leverage who wants to hurt you, simulating an attacker. It identifies exposed personal information, what data has been breached and more. Social media footprint, property records, business entities, data brokers, breached data, Street View, professional interviews and family members are investigated.
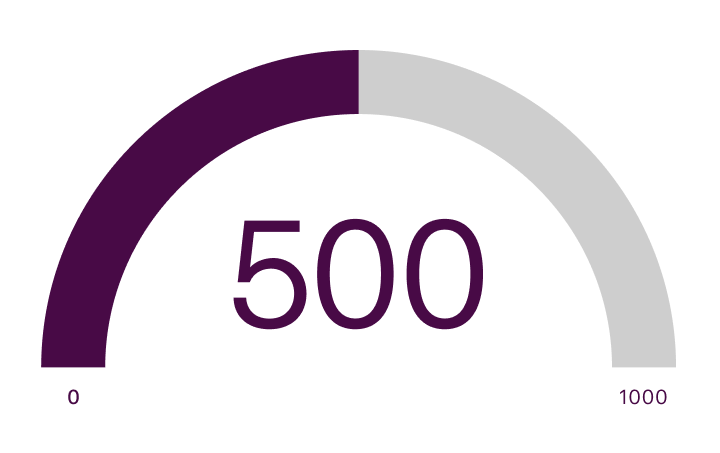
Your Risk in a Single Number
The combination of self-reported behaviors from the intake and observable exposures from OSINT produces data points used to calculate your Cyber Health Score.
This data model is the most rigorous approach for assessing how likely you are to fall victim to cyber attacks. Risk of phishing and spoofing, SIM swap, identity theft/financial crime, employment scam, malware and more are all accounted for. We also measure wealth, role, board seats and political involvement that may drive attackers to you. Because our goal to reduce your cyber risk, improving your Cyber Health Score underpins everything we do.
A Personalized Program, Just for You
Your onboarding concludes with your personalized Care Plan. This curated queue of software, security automations, monitoring and appointments with our team reduces is guided by your Cyber Health Score to address the specific cyber risks that impact you.
It is integrated into your dashboard and continuously updated as elements are completed and risks change.